Audit-Ready Cybersecurity for SOC 2, ISO 27001, and CMMC
Cybersecurity audits are no longer checkbox exercises. Regulators, customers, and auditors now expect demonstrable security controls, continuous monitoring, and evidence that aligns with recognized frameworks such as SOC 2, ISO 27001, and CMMC Level 2.
At ITSecOps.cloud, we support organizations through audit preparation, remediation, and ongoing compliance by aligning real security operations with audit expectations — not theoretical documentation.
What We Mean by “Cybersecurity Audit Support”?
-
- Readiness assessments against SOC 2, ISO 27001, and CMMC Level 2
-
- Security control implementation and validation
-
- Evidence collection and audit documentation
-
- Gap analysis and remediation planning
-
- Support during external audits and assessor walkthroughs
This approach ensures that security controls are implemented, enforced, and provable, not just documented.
Compliance Frameworks We Support
SOC 2 (Type I & Type II)
-
- Trust Services Criteria alignment
-
- Evidence mapping for CC6, CC7, CC8
-
- Continuous monitoring and incident readiness
ISO/IEC 27001
-
- ISMS-aligned security controls
-
- Annex A control implementation
-
- Risk treatment and audit evidence preparation
CMMC Level 2 (NIST SP 800-171)
-
- Control mapping and gap analysis
-
- Microsoft GCC and Azure environments
-
- Assessor-ready evidence and remediation
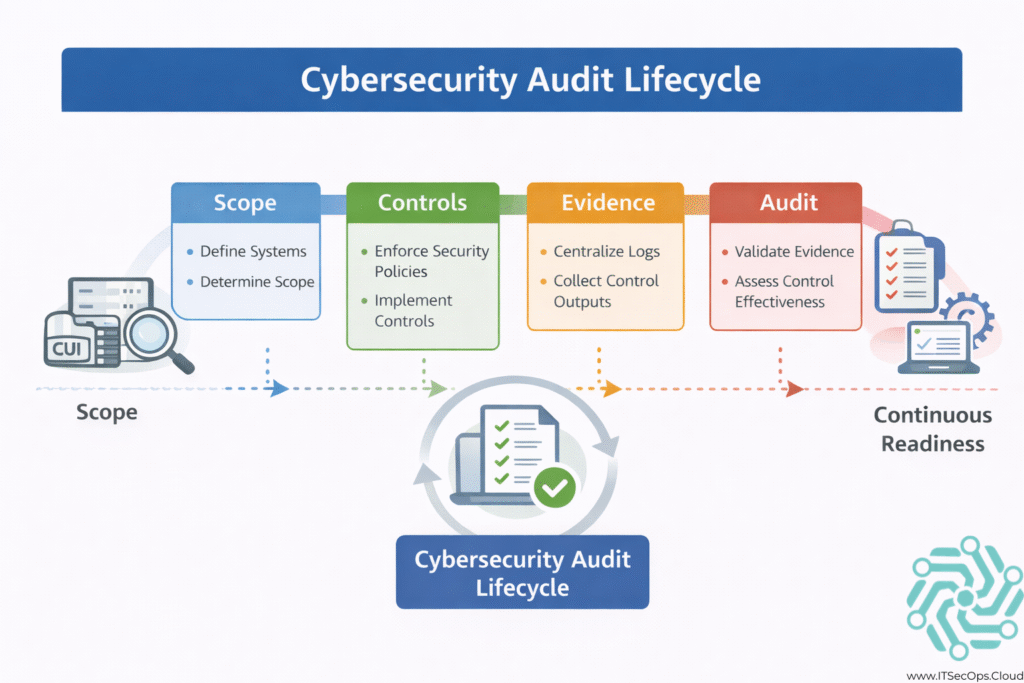
Our Audit-Focused Security Methodology
-
- Scope & Readiness Review
Identify applicable controls, systems, and audit boundaries.
- Scope & Readiness Review
-
- Control Validation
Ensure security controls are enforced in production environments.
- Control Validation
-
- Evidence Alignment
Map logs, configurations, and alerts to audit requirements.
- Evidence Alignment
-
- Remediation & Hardening
Address gaps identified during readiness or internal review.
- Remediation & Hardening
-
- Audit Support
Assist during external audits, assessor questions, and evidence reviews.
- Audit Support
Technology & Platforms We Work With
-
- Microsoft Defender (Endpoint, Identity, Office 365)
-
- Microsoft Azure & Azure AD
-
- Intune and Conditional Access
-
- Log analytics and security monitoring
-
- Cloud and hybrid IT environments
Tooling is only effective when it produces audit-consumable evidence — our focus is ensuring that security telemetry aligns with compliance requirements.
Who This Service Is For?
-
- SaaS companies preparing for SOC 2 audits
-
- Organizations pursuing ISO 27001 certification
-
- Defense contractors subject to CMMC requirements
-
- IT and compliance teams needing operational audit support
Why Organizations Choose ITSecOps.cloud
-
- Practitioner-led, audit-first approach
-
- Focus on real security operations, not templates
-
- Experience translating technical controls into auditor language
-
- Support across North America, Europe, and ANZ regions
Next Steps
If your organization is preparing for a cybersecurity audit or needs help aligning security operations with compliance frameworks, the next step is understanding where you stand today.
Our audit-focused approach helps organizations move from uncertainty to audit-ready confidence.
Related Services:
-
- SOC 2 Compliance Support
-
- ISO 27001 Compliance Services
-
- CMMC Level 2 Readiness