Audit-Ready SOC 2 Compliance Built on Real Security Operations
SOC 2 compliance is not achieved by documentation alone. Auditors evaluate whether security controls are implemented, enforced, monitored, and producing consistent evidence aligned with the Trust Services Criteria (TSC).
At ITSecOps.cloud, SOC 2 readiness is approached as an operational discipline, not a paperwork exercise. We support organizations in aligning real IT and security operations with auditor expectations, ensuring that controls withstand both Type I and Type II examinations.
This service is designed for organizations that want predictable audits, reduced disruption, and defensible evidence.
What SOC 2 Auditors Actually Evaluate
SOC 2 auditors focus on operating effectiveness, not intent. During an engagement, auditors typically validate:
- Logical access controls and MFA enforcement
- Endpoint protection and monitoring
- Security event detection and response
- Change management and administrative activity
- Incident handling and escalation workflows
- Evidence consistency across the audit period
Controls must demonstrate continuous enforcement, not point-in-time configuration.
SOC 2 Trust Services Criteria We Support
Security (Common Criteria – Mandatory)
- Access control enforcement
- Endpoint and identity protection
- Threat detection and alerting
- Incident response readiness
- Logging and monitoring
Availability (Optional)
- Monitoring and uptime controls
- Incident handling for service disruption
- Operational resilience evidence
Confidentiality (Optional)
- Data access restrictions
- Protection of sensitive information
- Evidence of data handling controls
Each criterion is mapped to real operational controls, not abstract policy statements.
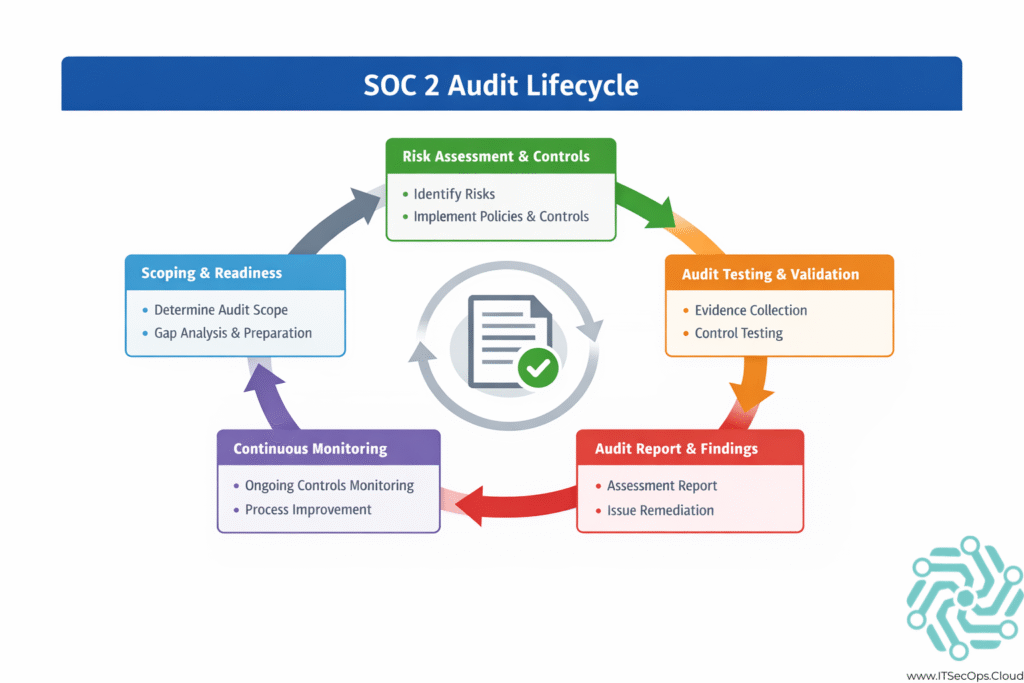
Our SOC 2 Compliance Methodology
SOC 2 readiness follows a structured, repeatable process designed to reduce audit risk.
1. Scope Definition & Readiness Assessment
- Identify in-scope systems, users, and data
- Align scope with Trust Services Criteria
- Identify gaps between current operations and audit expectations
2. Control Validation
- Verify enforcement of access controls
- Validate endpoint and identity security
- Confirm monitoring and alerting effectiveness
3. Evidence Alignment
- Map system-generated evidence to SOC 2 controls
- Validate evidence retention across the audit window
- Ensure traceability between controls and proof
4. Remediation & Hardening
- Address gaps in enforcement or monitoring
- Strengthen control explanations
- Reduce auditor follow-up risk
5. Audit Support
- Support auditor walkthroughs
- Assist with evidence requests
- Reduce operational disruption during the audit
SOC 2 Evidence: What Matters Most
Auditors prioritize clarity, consistency, and traceability.
| Control Area | Evidence Auditors Expect |
|---|---|
| Access control | MFA enforcement logs |
| Endpoint security | Protection status & alerts |
| Monitoring | Alert history & response |
| Change management | Administrative logs |
| Incident response | Tickets & timelines |
Well-organized evidence reduces audit duration and follow-up questions.
SOC 2 From an IT Operations Perspective
SOC 2 audits succeed when IT operations own enforcement and compliance teams own mapping.
From an operational standpoint:
- Controls must be enforced daily
- Alerts must be reviewed and responded to
- Logs must be retained and accessible
- Configuration drift must be managed
From an audit standpoint:
- Evidence must tell a consistent story
- Enforcement must be demonstrable over time
SOC 2 Type II audits expose operational weaknesses quickly — which is why ongoing readiness matters more than last-minute preparation.
SOC 2 Type I vs Type II: Operational Impact
SOC 2 Type I
- Validates control design at a point in time
- Focuses on whether controls exist and are configured
SOC 2 Type II
- Validates operating effectiveness over months
- Requires consistent enforcement and evidence retention
Organizations often pass Type I but struggle with Type II due to inconsistent operations.
When Organizations Need SOC 2 Support
External SOC 2 support becomes valuable when:
- Internal teams lack audit experience
- Evidence is fragmented across systems
- Controls exist but are inconsistently enforced
- Type II audits expose operational gaps
- Audit timelines are aggressive
Professional support reduces audit friction and improves outcomes.
How SOC 2 Fits Into a Broader Audit Strategy
SOC 2 controls often overlap with:
- ISO/IEC 27001
- NIST-aligned frameworks
- Cloud security best practices
Organizations that treat SOC 2 as part of a broader cybersecurity audit strategy reduce duplication and long-term compliance costs.
👉 Learn more about our cybersecurity audit support.
Who This Service Is Designed For
- SaaS organizations preparing for SOC 2 audits
- Companies undergoing SOC 2 Type II assessments
- CISOs and compliance managers seeking audit predictability
- IT teams responsible for security enforcement
This service is built for organizations that want audits to be defensible, repeatable, and operationally sound.
Frequently Asked Questions
How long does SOC 2 readiness take?
Timelines vary by scope and maturity, but readiness typically spans several weeks to months.
Does SOC 2 require specific tools?
No specific tools are mandated, but controls must be enforceable and auditable.
Can cloud-native environments meet SOC 2 requirements?
Yes, when controls are properly configured and evidence is retained.
What is the biggest SOC 2 failure point?
Inconsistent enforcement and missing evidence during the audit period.
Conclusion
SOC 2 compliance is a reflection of how security is operated day-to-day. Organizations that align IT operations, monitoring, and evidence collection early experience smoother audits and fewer disruptions.
Audit readiness is not achieved at the end of the process — it is built into operations.