CMMC Level 2 Compliance & NIST 800-171 Readiness Services
CMMC Level 2 Compliance Built on Enforced Security Controls
CMMC Level 2 compliance is not achieved through documentation, screenshots alone, or tool purchases. Assessors validate whether NIST SP 800-171 security controls are implemented, enforced, and producing consistent evidence across the environment.
At ITSecOps.cloud, CMMC Level 2 readiness is treated as an operational security program, not a certification exercise. We help organizations align real IT and security operations with CMMC assessment expectations, ensuring controls withstand assessor scrutiny.
This service is designed for organizations that want predictable assessments, minimal findings, and defensible evidence.
What CMMC Level 2 Assessors Actually Evaluate
CMMC Level 2 assessments are binary — controls are either met or not met. Assessors focus on enforcement and proof, not intent.
Assessors typically evaluate:
-
- Access control enforcement (users, devices, administrators)
-
- Endpoint protection and malware prevention
-
- Security monitoring and alert handling
-
- Configuration management and change control
-
- Incident response capability
-
- Log retention and evidence consistency
-
- Boundary protection and network security
Controls must demonstrate ongoing enforcement, not point-in-time configuration.
Understanding CMMC Level 2 and NIST SP 800-171
CMMC Level 2 maps directly to NIST SP 800-171, requiring implementation of all 110 controls across 14 control families.
Key characteristics:
-
- No partial compliance
-
- No compensating documentation
-
- Evidence must be assessor-ready
-
- Controls must operate continuously
CMMC Level 2 enforces operational security discipline, not theoretical compliance.
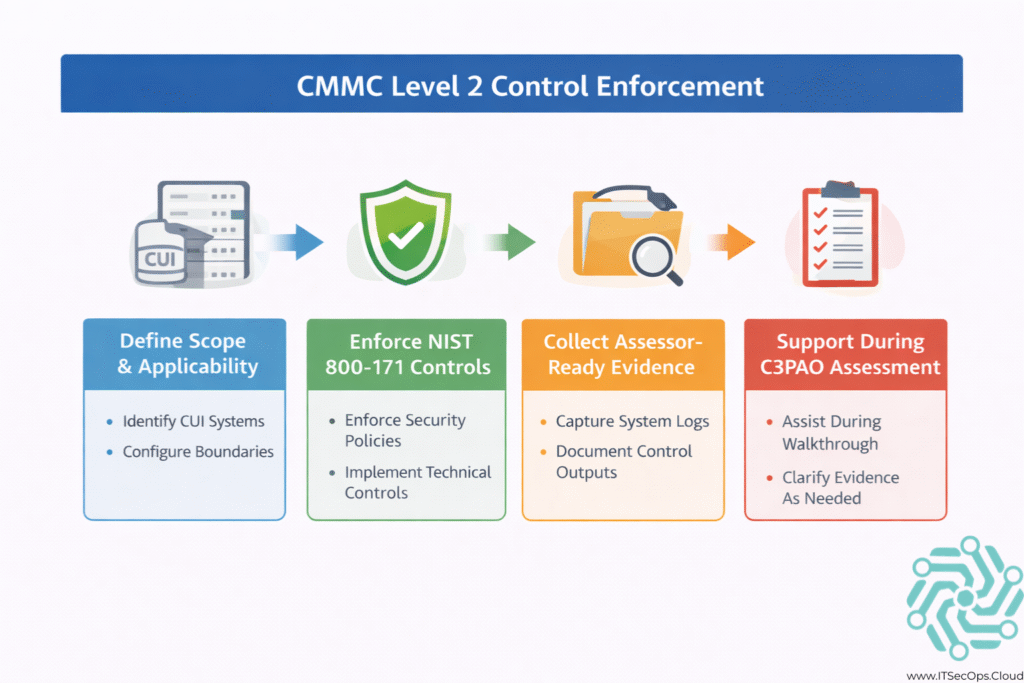
Our CMMC Level 2 Readiness Methodology
Our approach aligns NIST control requirements with real production environments.
1. Scope & CUI Boundary Definition
-
- Identify systems handling Controlled Unclassified Information (CUI)
-
- Define assessment scope and boundaries
-
- Validate data flows and dependencies
2. Control Gap Assessment
-
- Evaluate implementation against NIST SP 800-171
-
- Identify enforcement gaps and missing evidence
-
- Prioritize remediation based on assessment risk
3. Control Implementation & Hardening
-
- Enforce access control and MFA
-
- Harden endpoints and servers
-
- Configure monitoring and alerting
-
- Implement logging and retention
4. Evidence Alignment & Traceability
-
- Map evidence to each NIST control
-
- Validate consistency across the environment
-
- Prepare assessor-ready documentation
5. Assessment Support
-
- Support pre-assessment readiness reviews
-
- Assist during assessor walkthroughs
-
- Reduce operational disruption during assessment
NIST SP 800-171 Control Areas We Support
CMMC Level 2 requires coverage across all control families, including:
-
- Access Control (AC)
-
- Identification & Authentication (IA)
-
- System & Information Integrity (SI)
-
- Audit & Accountability (AU)
-
- Configuration Management (CM)
-
- Incident Response (IR)
-
- Risk Assessment (RA)
-
- System & Communications Protection (SC)
Each control must be implemented, enforced, and provable.
CMMC Evidence: What Assessors Expect
Assessors evaluate system-generated evidence, not narratives.
| Control Area | Evidence Assessors Validate |
|---|---|
| Access control | MFA enforcement & access logs |
| Endpoint security | Protection status & alerts |
| Monitoring | Security alerts & response |
| Configuration | Change logs & baselines |
| Incident response | Incident records & timelines |
Evidence must demonstrate consistency, enforcement, and scope alignment.
CMMC Level 2 From an IT Operations Perspective
From an IT operations standpoint, CMMC Level 2 compliance requires:
-
- Daily enforcement of security controls
-
- Continuous monitoring and alert response
-
- Configuration drift management
-
- Centralized logging and evidence retention
-
- Clear ownership of control responsibilities
CMMC assessments expose gaps quickly when operations are inconsistent or undocumented.
Common CMMC Level 2 Assessment Failures
Some of the most frequent assessment failures include:
-
- MFA enforced inconsistently
-
- Logs generated but not retained
-
- Controls applied outside the CUI boundary
-
- Incident response plans without evidence of execution
-
- Administrative access not monitored
-
- Incomplete or outdated SSP mappings
These failures are preventable with disciplined preparation.
CMMC Level 2 and Government Cloud Environments
Organizations operating in Microsoft GCC or similar environments must ensure:
-
- Identity and access controls align with NIST requirements
-
- Endpoint and workload protection is enforced
-
- Logs are accessible for assessor review
-
- Evidence reflects the correct tenant and scope
Government-regulated environments require extra care in evidence alignment.
How CMMC Fits Into a Broader Audit Strategy
CMMC Level 2 shares significant overlap with:
-
- SOC 2 security criteria
-
- ISO/IEC 27001 Annex A controls
-
- NIST-aligned cybersecurity programs
Organizations that treat CMMC as part of a broader cybersecurity audit strategy reduce duplication and long-term compliance cost.
👉 Learn more about our cybersecurity audit support.
Who This Service Is Designed For
-
- Defense contractors handling CUI
-
- Organizations preparing for CMMC Level 2 assessments
-
- IT and security teams responsible for NIST compliance
-
- Compliance managers supporting assessments
This service is built for organizations that need assessment-ready security, not paperwork.
Frequently Asked Questions
Is CMMC Level 2 mandatory?
Yes, for organizations handling CUI under DoD contracts.
Does CMMC Level 2 allow partial compliance?
No. All applicable NIST SP 800-171 controls must be met.
How long does CMMC Level 2 readiness take?
Timelines vary based on maturity, but typically span several months.
Do assessors require screenshots?
Yes. Screenshots and system-generated evidence are commonly reviewed.
Conclusion
CMMC Level 2 compliance demands operational security discipline. Organizations that enforce controls consistently, monitor effectively, and maintain assessor-ready evidence experience smoother assessments and fewer findings.
Compliance is not achieved at assessment time — it is demonstrated through daily operations.