Cybersecurity Audits Explained: SOC 2, ISO 27001, and CMMC
(Operator Guide for IT & Compliance Teams)
Introduction
Cybersecurity audits are no longer symbolic reviews driven by policy documents and spreadsheets. Modern audits are operational examinations that assess whether security controls are implemented, enforced, monitored, and capable of producing verifiable evidence aligned to recognized compliance frameworks.
Frameworks such as SOC 2, ISO/IEC 27001, and CMMC Level 2 require organizations to demonstrate not only intent, but execution. This guide explains how cybersecurity audits work in practice, what auditors actually validate, why many organizations fail audits despite having security tools in place, and how IT operations must support continuous audit readiness.
This is an operator-focused guide — written from the perspective of real IT security and compliance execution, not theory.
What Is a Cybersecurity Audit?
A cybersecurity audit is a structured assessment that evaluates whether an organization’s security controls meet the requirements of a defined framework and are operating effectively within the audit scope.
Audits are designed to answer three core questions:
-
- Are the required controls implemented?
-
- Are those controls consistently enforced?
-
- Can the organization produce evidence proving enforcement over time?
Policy vs Operational Evidence
A common misunderstanding is equating documentation with compliance.
-
- Policies define intent and expectations
-
- Operational evidence demonstrates execution
Auditors give limited weight to policies unless those policies are backed by real, system-generated proof such as logs, alerts, configurations, and incident records.
Why Tooling Alone Is Not Enough
Deploying security tools does not guarantee audit success. Auditors evaluate:
-
- Configuration accuracy
-
- Enforcement consistency
-
- Alert handling
-
- Evidence retention
-
- Control ownership
A deployed but unmanaged tool is often worse than no tool at all, as it creates false assurance.
Why Cybersecurity Audits Fail (Real Reasons)
Organizations rarely fail audits due to a complete absence of security tooling. Failures typically occur because controls exist only on paper or are not operationally enforced.
Common audit failure reasons include:
-
- Security controls exist but are not enforced
-
- Logs are generated but not retained
-
- Evidence does not clearly map to control requirements
-
- Security tools are deployed but not monitored
-
- IT operations and compliance teams work in silos
-
- Alert response processes are undefined or undocumented
-
- Evidence is scattered across systems without traceability
These failures are operational, not technical.
Common Cybersecurity Audit Frameworks
While cybersecurity audits differ by framework, they share a common expectation: continuous, provable control enforcement.
SOC 2
SOC 2 audits are based on the Trust Services Criteria (TSC), with Security as the mandatory category and optional criteria such as Availability and Confidentiality.
Key characteristics:
-
- Type I evaluates design at a point in time
-
- Type II evaluates operating effectiveness over a defined period
-
- Strong emphasis on monitoring, access controls, and incident handling
-
- Evidence must demonstrate consistent enforcement over the audit window
SOC 2 audits are evidence-heavy and operationally focused.
ISO/IEC 27001
ISO 27001 audits assess the effectiveness of an organization’s Information Security Management System (ISMS).
Key characteristics:
-
- Risk-based approach to control selection
-
- Controls defined in Annex A
-
- Emphasis on governance, risk treatment, and continuous improvement
-
- Auditors validate both management processes and technical enforcement
ISO audits often fail when risk assessments exist but are not reflected in operational controls.
CMMC Level 2
CMMC Level 2 aligns directly with NIST SP 800-171 and applies to organizations handling Controlled Unclassified Information (CUI).
Key characteristics:
-
- Mandatory enforcement of all 110 NIST controls
-
- Strong focus on endpoint security, access control, and monitoring
-
- Continuous enforcement required — not point-in-time compliance
-
- Evidence must be assessor-ready and traceable
CMMC audits are unforgiving of gaps in enforcement or documentation.
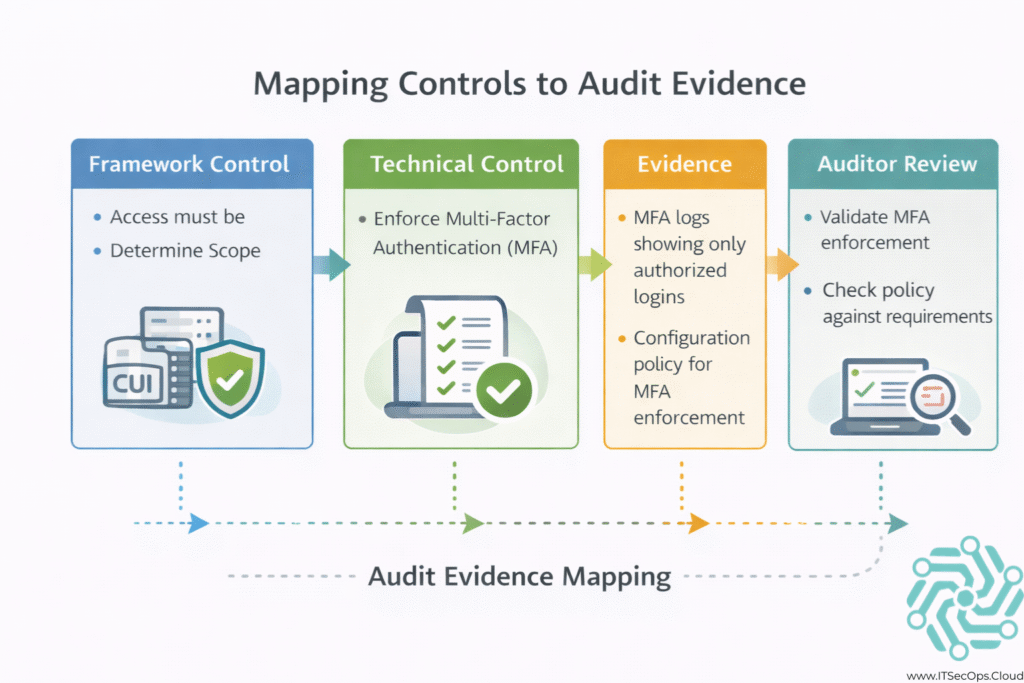
How Auditors Evaluate Security Controls
Auditors validate controls using a combination of methods. Interviews alone are never sufficient.
Auditors typically evaluate:
-
- Interviews with control owners and system administrators
-
- Screenshots of configurations and enforcement settings
-
- System logs showing real activity and alerts
-
- Configuration exports from security platforms
-
- Incident response records demonstrating detection and handling
Evidence must align directly to control objectives and be attributable to the audit scope.
Cybersecurity Audit Evidence: What Actually Matters
| Evidence Type | What Auditors Look For |
|---|---|
| Endpoint protection | Enforcement status and alert history |
| Identity controls | MFA enforcement and access logs |
| Monitoring | Alerts, response actions, and timestamps |
| Change tracking | Administrative and configuration logs |
| Incident handling | Tickets, timelines, and resolution evidence |
Auditors care less about how many tools you have and more about whether evidence tells a coherent operational story.
Cybersecurity Audits From an IT Operations Perspective
This is where many organizations succeed or fail.
From an IT operations standpoint, audits are not events — they are outcomes of consistent security operations.
Key IT SecOps responsibilities include:
-
- Ensuring security controls are enforced daily
-
- Monitoring alerts and responding consistently
-
- Maintaining log retention and accessibility
-
- Validating configurations after changes
-
- Supporting evidence requests without disruption
When IT operations own enforcement and compliance teams own mapping, audits become predictable instead of disruptive.
How Organizations Should Prepare for a Cybersecurity Audit
Effective audit preparation is operational, not administrative.
-
- Define Audit Scope
Identify systems, users, and data in scope early.
- Define Audit Scope
-
- Validate Control Enforcement
Confirm that controls operate as designed in production.
- Validate Control Enforcement
-
- Centralize Evidence
Ensure logs, alerts, and reports are accessible and retained.
- Centralize Evidence
-
- Fix Gaps Early
Address enforcement issues before the audit window begins.
- Fix Gaps Early
-
- Train Teams
Ensure staff understand audit expectations and evidence flow.
- Train Teams
Preparation should start months before an audit, not weeks.
Cybersecurity Audits vs Compliance Documentation
Documentation alone does not pass audits.
Auditors expect:
-
- Evidence of enforcement
-
- Proof of consistency
-
- Traceability between controls and systems
Documentation explains what should happen.
Evidence proves what is happening.
Organizations that treat audits as documentation exercises routinely fail operational reviews.
When to Involve External Audit Support
External support becomes valuable when:
-
- Internal teams lack audit experience
-
- Evidence mapping is unclear
-
- Controls exist but are inconsistently enforced
-
- Audit timelines are aggressive
Professional cybersecurity audit support helps organizations translate real security operations into auditor-ready evidence while reducing operational disruption.
Learn more about cybersecurity audit support.
Frequently Asked Questions (FAQs)
How long does a cybersecurity audit take?
Timelines vary by framework and scope. SOC 2 Type II audits typically span several months, while readiness assessments may take weeks.
What tools are commonly reviewed during audits?
Auditors review identity platforms, endpoint protection, monitoring systems, logging tools, and incident response workflows.
Do auditors require screenshots?
Yes. Screenshots are commonly requested to validate configurations and enforcement states.
How often should cybersecurity audits be performed?
Most frameworks require annual audits, with continuous monitoring expected between assessments.
Can cloud-native environments pass audits?
Yes. Cloud environments can meet audit requirements when controls are properly configured and evidence is retained.
Conclusion
Cybersecurity audits reward organizations that treat security as an operational discipline rather than a documentation exercise. Successful audits are the result of enforced controls, consistent monitoring, and clear evidence — not last-minute preparation.
Understanding how audits are conducted, what evidence matters, and how IT operations support compliance is the foundation of sustainable audit readiness.