ISO 27001 Compliance Built on Operational Security, Not Just Documentation
ISO/IEC 27001 certification is not achieved by writing policies or purchasing templates. Auditors assess whether an organization has established, implemented, maintained, and continuously improved an Information Security Management System (ISMS) that is operationally effective.
At ITSecOps.cloud, ISO 27001 compliance is approached as a governance-driven, risk-based operational program. We help organizations translate ISO 27001 requirements into enforceable security controls, repeatable processes, and defensible audit evidence.
This service is designed for organizations that want predictable certification outcomes, reduced audit friction, and an ISMS that actually supports the business.
What ISO 27001 Auditors Actually Evaluate
ISO 27001 auditors do not certify documents — they certify systems, processes, and evidence.
During an audit, assessors typically evaluate:
-
- Definition and scope of the ISMS
-
- Information security risk assessment methodology
-
- Risk treatment decisions and control selection
-
- Implementation of Annex A controls
-
- Evidence of operational effectiveness
-
- Management oversight and continual improvement
Auditors expect consistency between risk decisions, control implementation, and operational reality.
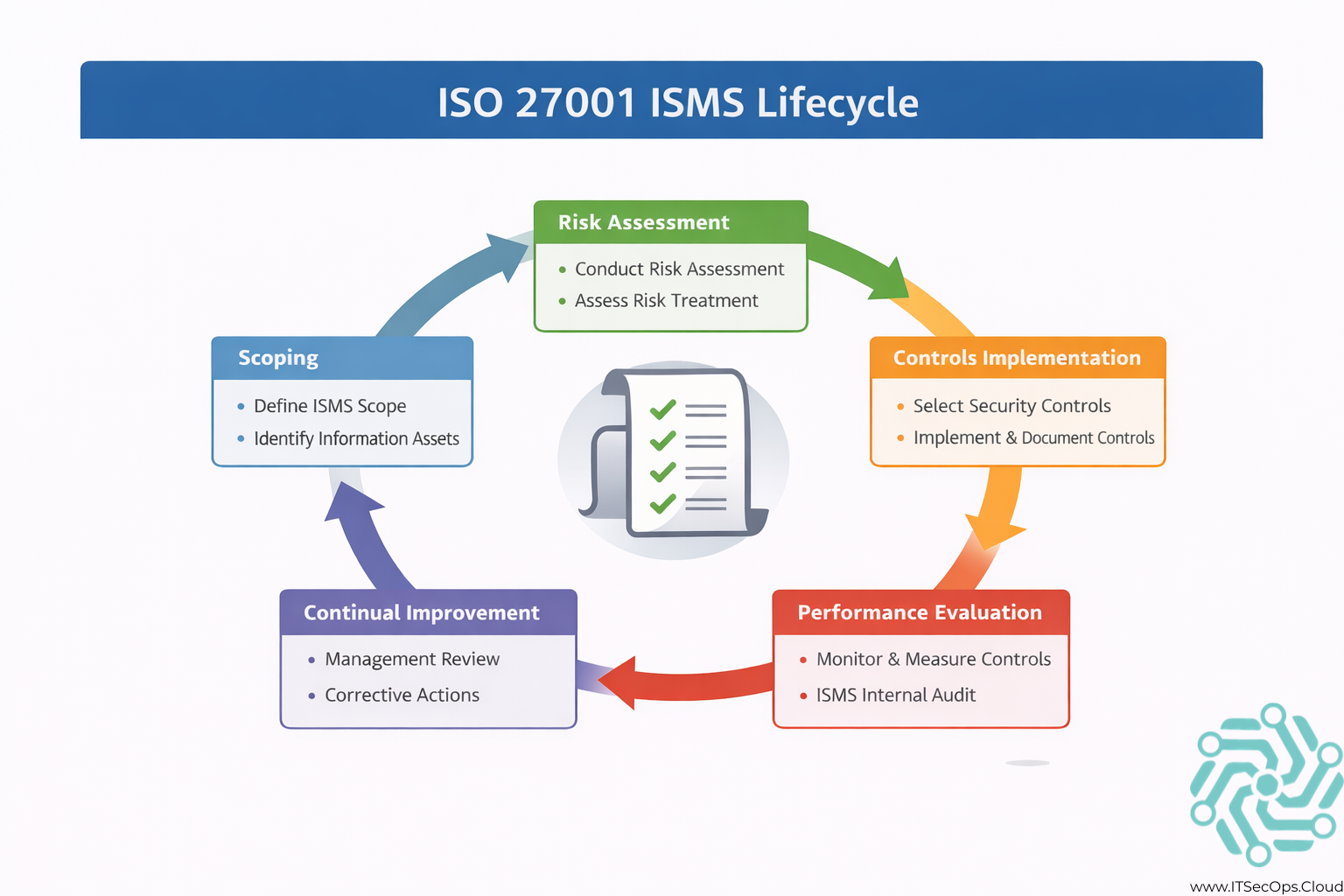
Understanding the ISO 27001 ISMS (In Practice)
An ISMS is not a static compliance artifact. It is a management system that governs how information security risks are identified, treated, monitored, and improved.
In practice, an effective ISMS includes:
-
- Clearly defined scope and asset inventory
-
- Documented risk assessment and treatment processes
-
- Enforced technical and administrative controls
-
- Defined roles and responsibilities
-
- Continuous monitoring and internal review
Organizations fail ISO audits when the ISMS exists in theory but not in daily operations.
ISO 27001 Annex A Controls: From Theory to Enforcement
Annex A controls provide a reference set of security controls. ISO 27001 does not require all controls — it requires justified selection based on risk.
Auditors validate:
-
- Why controls were selected or excluded
-
- How selected controls are implemented
-
- Whether controls operate as described
-
- Evidence that controls are reviewed and improved
Controls that are documented but not enforced are treated as audit failures.
Our ISO 27001 Compliance Methodology
Our approach aligns ISO requirements with real operational security.
1. ISMS Scope & Readiness Assessment
-
- Define organizational and technical scope
-
- Identify information assets and dependencies
-
- Assess current maturity against ISO 27001 clauses and Annex A
2. Risk Assessment & Treatment Design
-
- Establish risk assessment methodology
-
- Identify and evaluate information security risks
-
- Define risk treatment plans and control justification
3. Control Implementation & Validation
-
- Implement Annex A controls aligned to risk decisions
-
- Validate technical and procedural enforcement
-
- Ensure controls operate consistently in production
4. Evidence Alignment & Documentation
-
- Align operational evidence to ISO clauses
-
- Prepare Statements of Applicability (SoA)
-
- Validate audit traceability
5. Internal Audit & Management Review Support
-
- Prepare organizations for internal audits
-
- Support management review requirements
-
- Reduce findings during certification audits
ISO 27001 Evidence: What Auditors Expect to See
ISO auditors require evidence that the ISMS is operational and effective, not theoretical.
| ISMS Area | Evidence Auditors Review |
|---|---|
| Risk management | Risk registers & treatment plans |
| Access control | Enforcement records & logs |
| Incident handling | Incident records & response actions |
| Change management | Change logs & approvals |
| Monitoring | Review records & improvement actions |
Evidence must demonstrate consistency and governance.
ISO 27001 From an IT Operations Perspective
ISO 27001 certification succeeds when IT operations are aligned with governance decisions.
From an operational standpoint:
-
- Controls must be enforced daily
-
- Systems must reflect documented risk decisions
-
- Logs and records must be retained
-
- Changes must follow defined processes
From a management standpoint:
-
- Risks must be reviewed
-
- Controls must be reassessed
-
- Improvements must be documented
ISO 27001 is sustained through discipline, not effort spikes.
ISO 27001 Certification Timeline: What to Expect
Certification timelines vary based on scope and maturity.
Typical stages include:
-
- ISMS design and implementation
-
- Internal audit
-
- Management review
-
- Stage 1 audit (readiness)
-
- Stage 2 audit (certification)
Organizations that rush certification without operational readiness typically face findings and rework.
Common ISO 27001 Audit Findings
Some of the most frequent ISO audit issues include:
-
- Risk assessments not aligned to actual systems
-
- Annex A controls implemented inconsistently
-
- Lack of evidence for continual improvement
-
- Management review treated as a formality
-
- ISMS scope not reflected in operations
These issues are preventable with proper ISMS execution.
How ISO 27001 Fits Into Broader Compliance Programs
ISO 27001 aligns well with other frameworks such as:
-
- SOC 2
-
- NIST-based standards
-
- Industry-specific compliance requirements
Organizations that integrate ISO 27001 into a broader cybersecurity audit strategy reduce duplication and long-term compliance overhead.
👉 Learn more about our cybersecurity audit support.
Who This Service Is Designed For
-
- Organizations pursuing ISO 27001 certification
-
- Companies implementing or improving an ISMS
-
- CISOs and security leaders responsible for governance
-
- Compliance teams supporting certification audits
This service is built for organizations that want sustainable compliance, not one-time certification.
Frequently Asked Questions
Is ISO 27001 mandatory?
ISO 27001 is voluntary, but often required by customers or regulators.
Does ISO 27001 require specific tools?
No. It requires controls appropriate to risk, not specific technologies.
How often is ISO 27001 audited?
Certification involves annual surveillance audits and recertification every three years.
Can cloud environments achieve ISO 27001 certification?
Yes, when governance and controls are properly implemented.
Conclusion
ISO/IEC 27001 certification is a governance and operational challenge, not a documentation task. Organizations that align risk management, control enforcement, and continual improvement achieve predictable audit outcomes and long-term security maturity.
An ISMS that reflects reality is the foundation of successful ISO 27001 compliance.